THE FACTS ABOUT PHISHING
Deceptive emails are a threat in the workplace and at home
What would you do if a suspicious stranger came up to you on the street and tried to lure you down a dark alley? You’d probably sense danger and either walk away quickly or call for help.
But what if the stranger approached you through email? You might feel it’s safe to click on a link in the email or open an attached file — but it’s a trap.
Every day, cyber criminals use malicious emails to try to scam individuals and organizations — a type of attack known as “phishing.” Interacting with a phishing email carries serious risks for you, your employer, even your family and friends. Fortunately, everyone can learn tactics for recognizing and avoiding these attacks.
What Is Phishing
In a phishing attack, cyber criminals use deceptive emails to “fish for” information and lure people into falling for scams. These emails are carefully designed to trick you into revealing financial information, login credentials, or other sensitive data. Or, they may secretly install dangerous software (malware) that compromises your computer and the files on it.
Phishing emails typically pressure you to act quickly, without thinking. They play upon strong emotions – such as curiosity, fear, or greed. These psychological manipulation tactics are sometimes known as “social engineering.”
Phishing emails also use a variety of technical tricks to steal information:
- Malicious web links – You’re asked to click on a link that takes you to an imposter website or to a site infected with malware.
- Malicious attachments – You’re urged to open an unexpected attachment that contains malware.
- Fraudulent data-entry forms – You’re prompted to fill in sensitive information like user IDs, passwords, credit card data, and phone numbers.
Is Phishing Really My Problem?
Many companies have suffered serious data breaches that exposed everything from business secrets to the confidential data of millions of people. These data breaches often start by tricking one person with a phishing email, giving criminals a foot in the door.
Phishing can affect your personal life, too. Whether at home or at work, falling for a phishing email can have serious, long-term consequences.
The Consequences of Falling for a Phish |
|
|
At Work |
In Your Personal Life |
|
• Loss of university funds • Exposed personal information of students and coworkers • Outsiders accessing confidential communications, files, and systems • Files becoming locked and inaccessible • Damage to the university’s reputation |
• Money stolen from your bank account • Fraudulent charges on credit cards • Tax returns filed in your name • Loans and mortgages opened in your name • Lost access to photos, videos, and files • Fake social media posts made in your accounts |
What Can I Do?
- Develop your anti-phishing skills. Enroll in the security awareness training program either through the university Bridge or Security Education Platform. (Security Education Platform accessible through Firefly) This is a great way to learn the warning signs of a phish and other social engineering tactics.
- Report it!
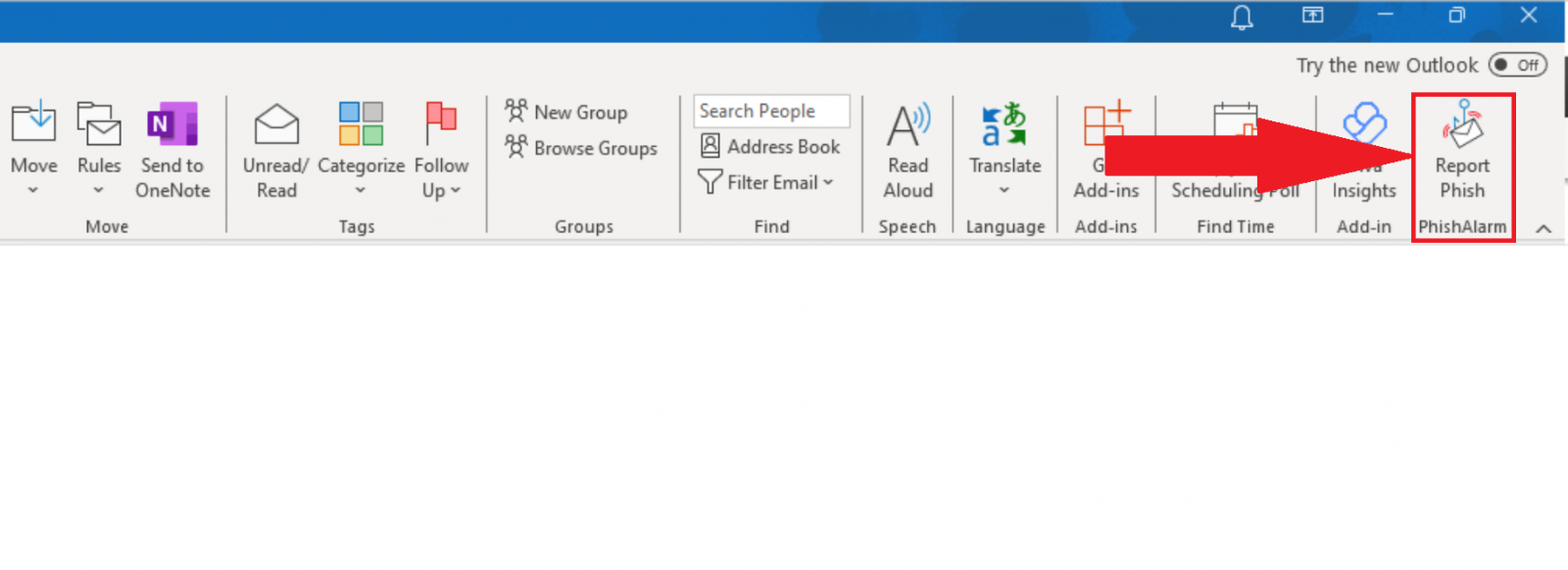
Report a Phish from Outlook desktop client:
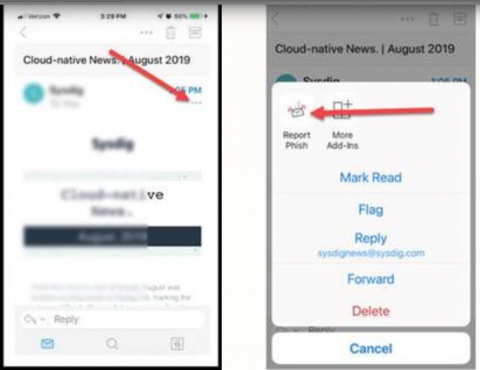
Report a Phish from Outlook Mobile, when the email is open on your phone, select the ellipsis of the email, then select REPORT PHISH:
Tips for Family and Friends
Share what you’ve learned about phishing and ask family and friends about their cybersecurity knowledge or experiences.
- Think before you click – You shouldn’t automatically trust any email message, especially if it sounds frightening or too good to be true. Familiar logos, senders’ names, and personal information are often faked by scammers.
- Be wary of unexpected requests for personal information – Never send account numbers, PINs, or login credentials through email — even if the request sounds urgent.
- Verify attachments before opening or downloading – Even if an email seems to come from a company or person you trust, don’t open an unexpected attachment. To make sure the file is legitimate, contact the company or individual directly through its website or use a known, verified phone number.